Security at eCourtDate
Hardened SaaS application security for government cloud workloads
Firewall and DDoS protection

Hosted in the CJIS-compliant AWS GovCloud™

Single Sign On with Azure and Office365
Government-grade Encryption
HTTPS is enforced in transit and AES 256-bit encryption at rest. This applies to data received by users as well as data stored or transmitted in internal systems. All requests require a secure connection.
Multi-Tenant Serverless Architecture
We use a distributed, serverless cloud-native architecture for maximum security, performance, and capability. Each agency is assigned an isolated tenant based on their optimal GovCloud region.
Role-based Access Control
Configure user access on a granular level with customizable roles and permissions. Assign Create, Read, Update, or Delete permissions based on each record type.
Multi-factor Authentication
MFA is required with app and hardware based support.
API Key Management
Create and manage secure and expirable API keys.
Disaster Recovery
Automated rollover and hourly data backups ensure 99.95% uptime.
eCourtDate is proud to be a member of the GovRAMP cybersecurity community. We are listed in the Progressing Product list here.
Compliance & Standards
eCourtDate maintains a comprehensive compliance program aligned with the most rigorous government security standards. Our security controls and assessments are reviewed annually to ensure ongoing compliance.
CJIS Security Policy — Designed to meet the FBI's Criminal Justice Information Services security requirements
FIPS 140-2/140-3 — Platform operates using AWS FIPS 140-2/140-3 validated cryptographic services
CSA STAR Level One — Cloud Security Alliance Security Trust Assurance and Risk registry
CISA Cyber Resilience Review (CRR) — Assessment aligned with CISA best practices
GovRAMP Member — Listed in the GovRAMP cybersecurity community Progressing Product list
ISO 27001-Aligned — Information security management system based on ISO 27001:2013 guidance
HIPAA — eCourtDate can be configured to support HIPAA-compliant workflows for agencies handling protected health information
Annual Penetration Testing — Independent third-party penetration tests and vulnerability assessments conducted annually; reports available upon request under NDA
How We Secure Your Data
Securing your data is a critical responsibility, and ensuring its protection is at the core of everything we do. We combine expertise, vigilance, and automation to keep data protected. We are happy to answer any of your questions regarding our security practices.
Data Integrity
Backups occur via continuous streaming replication and frequent snapshots. We can restore to a point-in-time or reprocess integration sources based on time received. We use AWS RDS for automated data encryption and point-in-time backups.
Account
We offer integration with third-party authentication services like Office 365, Google, LinkedIn, OAuth 2.0, and LDAP. You can enforce password policies for your internal users based on granular permission policies.
Password Security
We employ the latest CJIS-compliant password security policies including authenticated, encrypted channels for password requests, failed attempt limits, and forced password changes.
Data Reset Tools
We provide a "Reset Data" tool that allows authorized administrators to permanently delete records based on type. An email alert is sent and users can access each agency directly to verify that the data is deleted. Cached data sources are immediately purged upon using the reset tool.
Continual Monitoring
Our support team continuously monitors the performance and integrity of our services, including intrusion attempts, via automated monitoring. We run OWASP Top 10 and CWE/SANS Top 25 scans automatically on all code version changes, daily PCI and SSL compliance scans, and automated DNS and firewall scans using CloudFlare.
Application Security
We employ cutting-edge, leading industry methods to protect our applications including deployment of sophisticated malicious bot detection, malicious file scanning to detect trojans, viruses, and malware, and automated vulnerability scans.
Physical Security
We host eCourtDate on AWS GovCloud (US). GovCloud data centers host sensitive data and regulated workloads and address the most stringent US government security and compliance requirements.
Data Backup Tools
We provide a "Backup Data" tool that allows authorized administrators to bulk export raw data in JSON, CSV, and SQL formats. This can be used in advance of running the "Reset Data" tool.
Third-Party Integrations
All third-party integrations are geo-restricted, IP restricted, and use modern protocols with support for secure connections (HTTPS, SSH). Any automated security alerts, including warnings such as unexpected logins, are sent to authorized users.
Network Security
We use best practices for DNS security, including DNSSEC, DKIM, DMARC, and SPF. This includes domain authentication methods for email delivery. We use CloudFlare for DDoS protection and Web Application Firewall. Our bug bounty program invites researchers and customers to conduct penetration tests at any time.
Employee & Organizational Security
eCourtDate maintains rigorous personnel security standards to ensure that all employees who access, manage, or support government data meet the highest levels of trust and accountability.
All employees are United States-based and undergo comprehensive background checks prior to employment
Employees handling Criminal Justice Information (CJI) complete CJIS Security Awareness Training and are fingerprinted in accordance with CJIS policy
All staff complete annual security awareness training covering phishing, social engineering, data handling, and incident reporting
Access to production systems follows the principle of least privilege and is reviewed quarterly
All subcontractors and third-party vendors are required to execute security and privacy agreements and meet equivalent security standards
Employees sign confidentiality and non-disclosure agreements as a condition of employment
Identity, Authentication & Password Management
eCourtDate provides enterprise-grade identity and access management to meet the security requirements of government agencies.
Single Sign-On (SSO)
We support SAML 2.0, OAuth 2.0, LDAP, Active Directory, Azure AD, Google Workspace, and Office 365 for seamless integration with your existing identity provider.
Multi-Factor Authentication
MFA is required for all administrator and privileged access. We support app-based authenticators (TOTP), hardware security keys (FIDO2/WebAuthn), and SMS-based verification.
Password Policy
CJIS-compliant password policies are enforced including: minimum 20-character length with complexity requirements, 90-day expiration with 10-password history enforcement, account lockout after consecutive failed attempts, and secure self-service password reset.
Account Provisioning
User accounts are provisioned and deprovisioned through administrative controls with full audit trails. Automated deprovisioning is supported via SCIM and directory sync to ensure timely access removal.
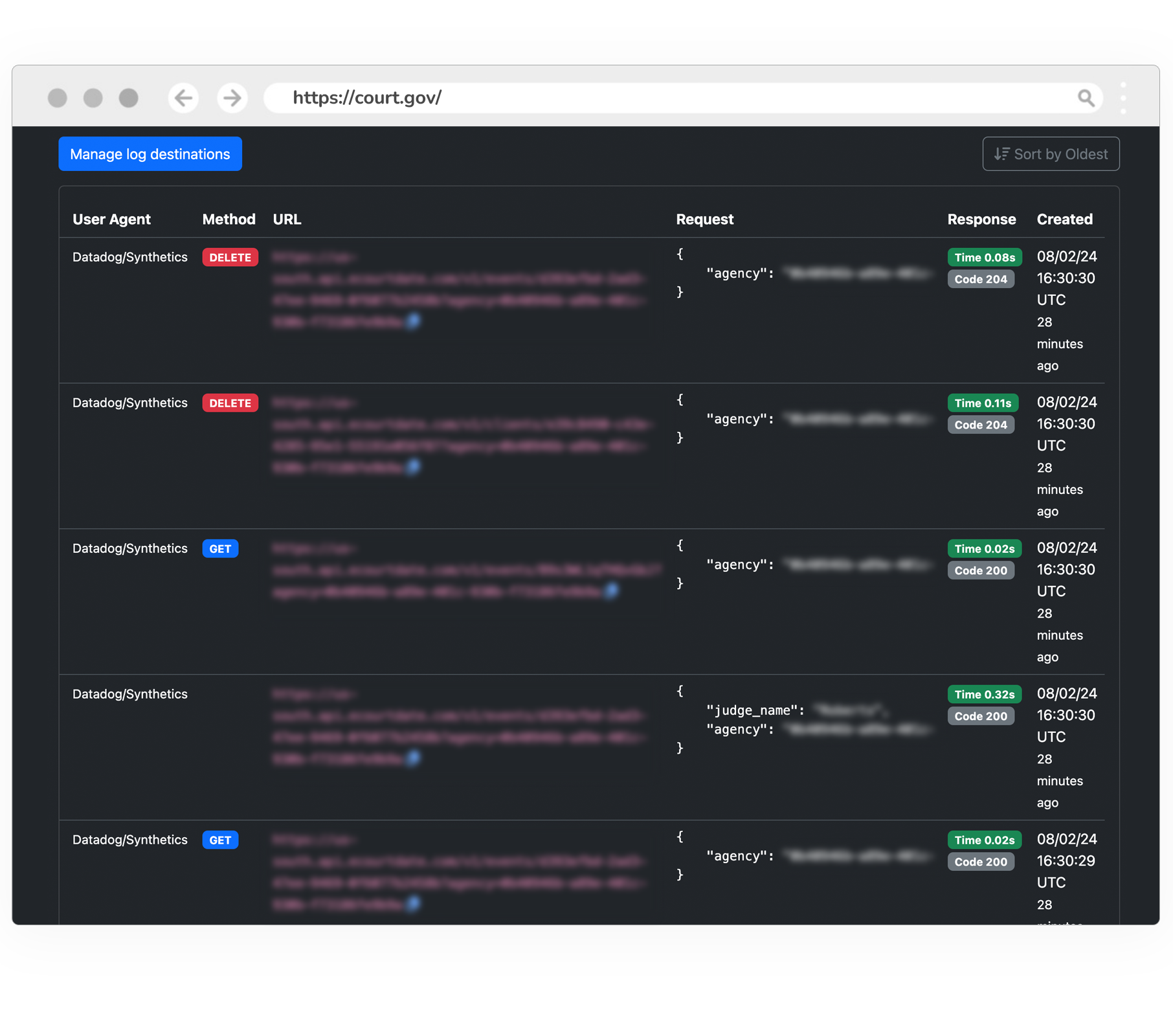
User Audit Logs
Track all user activity in real-time with read-only audit logging.
User activity is stored in encrypted audit logs which are available for the duration of the contract. Authorized users can search real-time and historical records, and logs are downloadable in CSV, JSON, and XML formats. Audit logs are "Read Only" regardless of user type or permission and available for the duration of the contract. We do not allow for any modification or deletion. Audit Logs can only be accessed through our console application which is restricted to administrator users. In addition, we log all system access using GovCloud CloudTrail for overall monitoring and security compliance. All logs are uniquely identified based on the user identifier with created, updated, and last active timestamps. All failures and error logs are part of our audit logs. In addition, any unexpected process failures are sent to administrators as an email "System Issue" notification.
Privacy Mode
All data is encrypted in transit and at rest. For customers with sensitive data such as juvenile and victims services, we offer an enhanced Privacy Mode which enables the following Personal Identifiable Information (PII) and Multi-factor Identification (MFI) protections:

PII fields are hidden by default when users interact with the application.
PII records are automatically archived after the data is inactive.
Archived data is automatically purged after a defined period (typically 90 days).
Any PII fields in data reports can redacted or masked.
We do not store any PII fields on portals or data dashboards in general.
Clients and message recipients are required to perform MFA with sessions limited to 1 hour.
Federal Information Processing Standard (FIPS 140-2/140-3) Compliant
Built to meet the rigorous security requirements of Federal Information Processing Standards (FIPS).
We use AWS's FIPS 140-2/140-3 compliant cryptographic services, ensuring that all data encryption, decryption, and key management processes adhere to federal and state standards.
Our platform is hosted in AWS GovCloud (US), a secure environment specifically designed for U.S. government workloads. This ensures that all data is processed and stored using FIPS-compliant endpoints, providing an additional layer of protection for sensitive information.
To maintain compliance, we continuously monitor our systems and perform regular audits.

Backup & Disaster Recovery
eCourtDate maintains comprehensive backup and disaster recovery capabilities to ensure data durability and business continuity for all agency partners.
Backup Strategy
Data is protected through continuous streaming replication and hourly encrypted snapshots. All backups are stored in AWS GovCloud (US) with AES 256-bit encryption. Point-in-time recovery is supported with a retention period of 30 days for snapshots and 7 days for continuous replication logs.
Disaster Recovery
Our disaster recovery plan includes multi-region failover within AWS GovCloud, tested on a quarterly basis. Recovery Time Objective (RTO) is 4 hours and Recovery Point Objective (RPO) is 1 hour for critical systems.
Uptime & Availability
eCourtDate guarantees 99.95% uptime as part of our Service Level Agreement. Our distributed, serverless architecture is designed for high availability with automated failover and self-healing capabilities.
Data at Contract Termination
Upon termination of an agreement, agencies may export all data in standard formats (JSON, CSV, SQL) using our Backup Data tool. Following data export and confirmation, eCourtDate performs certified secure deletion of all agency data, including backups, within 30 days. A certificate of data destruction is provided upon request.
Incident Response
eCourtDate maintains a dedicated Incident Response (IR) team to ensure rapid detection, containment, and resolution of security incidents.
IR Team & Coordination
Our IR team is headed by a designated IR Coordinator responsible for documenting and executing incident response procedures. Proactive measures are taken to prepare for likely incidents rather than relying on decisions made during a crisis.
Notification & Communication
In the event of a security incident affecting customer data, eCourtDate will notify affected parties within 24 hours of confirmed impact. Notification includes the nature of the incident, data affected, remediation steps taken, and ongoing communication until resolution.
Incident Prioritization
- P0 Critical — Catastrophic impact requiring immediate response and maximum resources
- P1 High — Major operational disruption until resolved
- P2 Moderate — Noticeable impact but operations continue with prompt resolution
- P3 Low — Minimal impact, managed through standard risk processes
Law Enforcement Coordination
Incidents involving customer data may require coordination with law enforcement and external agencies. eCourtDate cooperates fully with authorized investigations while maintaining data confidentiality.
Data Center Security


Monitoring, Patching & Maintenance
eCourtDate employs continuous monitoring and proactive maintenance to ensure the security, performance, and reliability of all systems.
24x7 Monitoring
Infrastructure and application health are monitored around the clock using Datadog, AWS CloudTrail, Amazon GuardDuty, and Cloudflare analytics. Automated alerts trigger immediate response for anomalies, performance degradation, and potential security threats.
Vulnerability Management
Automated vulnerability scans run continuously via DeepSource, OWASP Top 10, and CWE/SANS Top 25 frameworks. Daily PCI and SSL compliance scans are performed, along with routine DNS and firewall assessments. Annual third-party penetration tests supplement automated scanning.
SIEM Integration
eCourtDate supports log forwarding to agency Security Information and Event Management (SIEM) systems upon request. All system, access, and security logs are available for integration with your existing security operations center.
Patching Cadence
Critical security patches are applied within 24-48 hours of release. High-severity patches are applied within 7 days. Routine patches and updates follow a defined monthly schedule. All patches are tested in staging environments prior to production deployment.
Maintenance Windows
Planned maintenance is scheduled during low-traffic windows with a minimum of 2 weeks advance notice to affected agencies. Emergency maintenance for critical security issues may occur with shorter notice, accompanied by real-time status updates.
Infrastructure Strategy
eCourtDate continuously evaluates and upgrades infrastructure to meet evolving security standards and compliance requirements. Our serverless, cloud-native architecture enables rapid adoption of new security capabilities without disruption to agency operations.
Support & Service Levels
eCourtDate provides dedicated, US-based support to ensure agencies receive responsive assistance at every stage.
24x7 Support
Support is available around the clock via phone, email, web portal, and live chat. Our US-based support and engineering teams are trained in CJIS-compliant data handling and government technology requirements.
Dedicated Account Manager
Each agency is assigned a dedicated account manager who serves as a single point of contact for onboarding, training, ongoing support, and strategic planning.
Escalation Procedures
Structured escalation paths ensure that critical issues are elevated to senior engineering and management within defined timeframes. Agencies can request escalation at any time through their account manager or the support portal.
Service Level Agreement
eCourtDate guarantees 99.95% platform uptime. SLA terms include defined response times based on issue severity, proactive monitoring with automated alerting, and monthly uptime reporting available upon request.
Security Assessments
Software Bill of Materials
Third-party vendors that we use to operate the eCourtDate platform.
Amazon Web Services
We use Amazon Web Services as an IaaS (infrastructure-as-a-service) provider.
Microsoft Azure
We use Azure as an IaaS (infrastructure-as-a-service) provider.
GitHub
We use GitHub to manage our source version control.
CloudFlare
We use CloudFlare for our content delivery network and DDoS protection.
Postman
We use Postman to design and test our APIs.
Auth0
We use Auth0 to handle authentication for our users.
DataDog
We use Datadog to monitor our infrastructure health.
Let's Encrypt
We use Let's Encrypt to provision our SSL certificates.
Continuous Code Health
We use DeepSource and other continuous monitoring technology to ensure secure code design and dependencies.
View ReportSecurity FAQs
Frequently Asked Questions
Comprehensive answers to common government security questionnaire topics.
General & Compliance
Hosting & Infrastructure
Data Protection & Encryption
Access Control & Authentication
Monitoring, Auditing & Incident Response
Employees & Operations
Network & Application Security
Are You A Security Researcher?



